Microsoft’s Hyper-V Server 2019 Finally Released After being plagued with everything from data loss issues to a lack of available hardware, Microsoft finally released their long-awaited Hyper-V Server 2019 to their Evaluation Center approximately eight months after the expected release date of October 2, 2018. This is even after the Microsoft team skipped the crucial RTM (“release-to-manufacturing”) […]
Category Archives: Our Blog
You know running a successful business requires much more than just offering a great product or service. It takes constant engagement and collaboration of all of your employees to produce the best results, and it takes your best effort to remain competitive in a crowded marketplace. Collaboration between employees used to mean lots of daily […]
There are everyday warriors in businesses across the country, but these individuals may never have worn the uniform of their country. This next generation of cyber warriors is being groomed by organizations of all sizes in an attempt to overcome the growing skills gap in the cybersecurity world. While many current cybersecurity analysts started in […]
Cybersecurity is now a priority for small and mid-sized businesses in Dallas. It’s no longer an afterthought, but at the foremost forefront. With the right Dallas IT support company, cybersecurity doesn’t have to be complicated. Here are 12 steps you can take now to increase your business IT security
Have you ever wanted to put access to certain apps on your phone or tablet under an extra layer of security? There are all sorts of reasons people might want this. Maybe you want to share your phone with a child, but you don’t want little Johnny messing with work apps or your grown-up Netflix […]
Got Your Sparklers Handy? The Fourth of July falls on a Thursday this year, but we aren’t letting the fact that it’s a weekday stop us from celebrating. Of course, just because it’s a holiday, that doesn’t mean you’ll have to make do without us. You’ll be able to reach us at {phone} […]
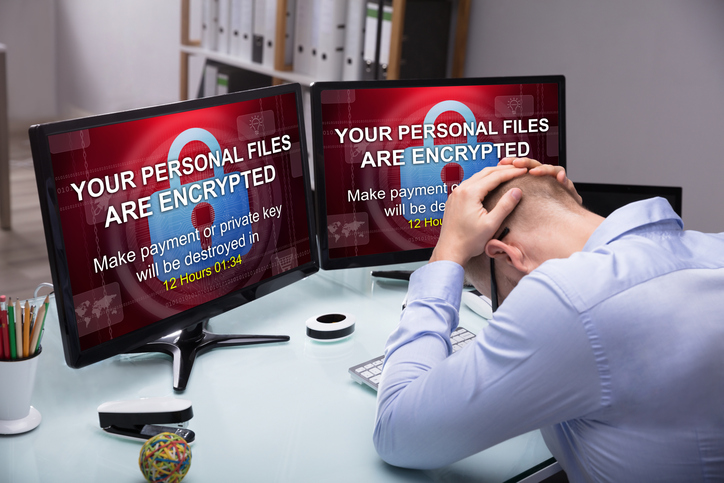
Cybercriminals lock victims out of computer and network files – sometimes destroying data – and extort cash to get that data back. That’s a ransomware attack, costing businesses billions worldwide. Ransomware can spread by the simplest of user actions. Email phishing, or Business Email Compromise (BEC) – fraudulent and deceptive emails posing as legitimate messages – is […]
Organizations across the country are learning from cyber attacks perpetrated in Atlanta, Newark, and Sarasota. Similarly, large targets such as San Francisco’s transit authority and Cleveland’s airport have also been targeted. The growing threat from ransomware, which locks up the victim’s device and files, is hard to track down to the source. Fortunately, many attacks […]
Every business should have a comprehensive cybersecurity plan and a competent team that can execute that plan. Otherwise, cybercriminals and malicious actors can and most likely will take advantage of security vulnerabilities to access company data and cause damage. But as important as it is to have skilled IT professionals looking out for your business, […]
This article covers the definition of metadata and how to view, manage and delete it in Microsoft applications. What is Metadata? Metadata is information about your data. It contains facts that can’t be disputed, the same way data does. Here is an example from Microsoft Word. Let’s say you’re writing a letter to a co-worker. […]